Overview – DDoS
You will be attacked; it is only a matter of time and time and DDoS is only one method.
Consider DDoS, Distributed Denial of Service attacks. The following information is extracted from a VeriSign report, VERISIGN DISTRIBUTED DENIAL OF SERVICE TRENDS REPORT. The full report can be found at: https://www.verisign.com/assets/report-ddos-trends-Q42016.pdf
Attackers in Q4 2016 launched sustained and repeated attacks against their targets. Verisign observed that more than 50 percent of customers who experienced DDoS attacks in Q4 2016 were targeted multiple times during the quarter.
Overall, average attack peak sizes in 2016 were larger than previous years. In fact, Verisign observed an average attack peak size of 16.1 Gbps in 2016, a 167 percent increase from 2015, in which the average attack peak size was 6.02 Gbps.
Highest Intensity Flood and Largest Volumetric Attack
The largest and highest intensity DDoS attack observed by Verisign in Q4 2016 was a multi-vector attack that peaked at over 125 Gbps and around 50 Mpps. The attack was notable because attackers were persistent, sending attack traffic on a daily basis for almost an entire month. The attack consisted of DNS Reflection traffic and Internet Control Message Protocol (ICMP) traffic and the attackers switched periodically to TCP SYN and TCP Reset floods peaking at approximately 70 Gbps and 50 Mpps. The attack also included floods of IP fragments to increase the volume of the attack.
DDoS Attacks Against Public Sector Increases
In Q4 2016, public sector customers experienced the second highest number of DDoS attacks among the Verisign DDoS Protection Services customer base (32 percent of total attacks). This is the highest percentage of DDoS attacks that Verisign has observed against Verisign public sector customers since the inception of the Verisign DDoS Trends Report in Q1 2014. Customers in the IT Services/Cloud/SaaS industry continue to have the largest number of DDoS attacks in Q4 2016.
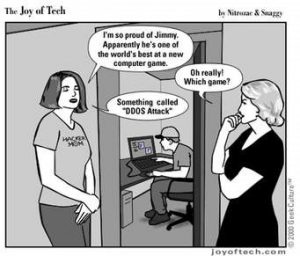
MARKET LANDSCAPE: THE BOTNET ECOSYSTEM
Launching a DDoS attack is much more accessible to attackers thanks to the rise of cloud computing, cheap hosting, readily available bandwidth and open-source attack tools. From low-skilled teenagers aiming to cheat while playing online games to cybercriminals looking to supplement their income by renting out their botnets for opportunistic attacks, the DDoS-for-hire market is booming.
The Botnet Ecosystem
Botnets utilized in DDoS attacks vary greatly in size and potency, from as small as a dozen compromised computers to as large as over one million devices. For example, a recent DNS-based DDoS attack that caused significant portions of the east coast of the United States to experience connectivity issues to certain websites involved a flood of malicious requests from up to 100,000 malicious endpoints.2 Botnets are comprised of computers, smartphones, servers, routers, printers and even IoT devices like networked refrigerators. With more devices continuously connected to the internet, the available pool of devices that could be used as botnets has increased. Attackers can now rapidly identify and leverage thousands of compromised devices and harness their bandwidth to launch DDoS attacks that can overwhelm even the most prepared networks.
Mitigating DDoS Attacks by Botnets
Because most DDoS-for-hire services frequently share similar characteristics, identifying popular DDoS techniques can help companies mitigate and defend against a variety of DDoS attacks. However, there still is a human element involved. Since most DDoS attacks are concerted efforts by live attackers to bring down a network, many of the attacks start out as one type of attack, but then morph into something new or different. Consequently, organizations need to have access to a high level of expertise and experience in combatting these complex hybrid DDoS attacks. Having a solution that includes monitoring of traffic behavior, the ability to defend against not only network, but also application layer attacks, and the flexibility to transfer large attack traffic to a cloud-based DDoS provider can help to alleviate dangerous threats and costly attacks.
Send me an email to tom@trholthus.com with your phone number if you want to learn more about information security.

1 comment
Very educational and informative.
Thanks for posting this.
This is why I think it’s important to not put all your eggs in one basket.
E.G. my web host doesn’t handle my email accounts, google apps does.
My email host, google apps, doesn’t handle my email distribution. Convertkit handles that.
Convertkit doesn’t handle my landing pages, Optimess press on my wordpress blog handles that.
I will admit that I don’t have redundant layers for each level, e.g. if google apps goes out my mail is out. I should figure out how to leverage office for business as a backup.
Multi factor authentication is also an important factor to be aware of.
Especially in this day and age.
Not only can a DDOS attach take your business down, however someone acting on your behalf without you knowing about it can also have devastating results.
Damashe and myself talk all about 2 factor in next Tuesdays Damashe and Michael, Just talking tech (DM Series) podcast episode, I hope you’ll give it a listen…
Oh yea, and you know, it’s a lot harder to get into an account if your not using the same password. 1Password is what we talked about on this past tuesday, click my name to listen to that episode.
thanks again for posting.